LLM traffic converts 3× better than Google search
58% of buyers now start their research in ChatGPT or Gemini, not Google. Most startups aren't showing up there yet.
The ones that are get cited by the AI tools their buyers, investors, and future hires already use. And they convert at 3×.
Download the free AEO Playbook for Startups from HubSpot and get the exact steps to start showing up. Five minutes to read.
Over the last ~72 hours, threat signals converged on five patterns: active exploitation of end-user software (PDFs), pre-auth RCE in developer notebook platforms, critical network OS vulnerabilities with device-takeover potential, fresh consumer breach exposure feeding credential abuse, and publicly leaked exploit code that accelerates copycat exploitation.
The operational takeaway: if you’re not enforcing patch SLAs on endpoints and “internal-only” tooling, attackers will keep turning routine actions (opening a PDF, visiting an internal notebook, managing network gear) into initial access.

Trend (Macro) | Likelihood | Direction | Signal for the Week |
|---|---|---|---|
“Open-a-file” endpoint exploitation (PDF / Reader chains) | 82% | 🔺 Rising | Real-world exploitation pressure is driving emergency patch windows. |
Pre-auth RCE in dev / data tooling (notebook platforms) | 78% | 🔺 Rising | Weaponization speed is extremely high once PoC drops. |
Network OS takeover risk (router/switch/firewall operating systems) | 72% | 🔺 Rising | Critical remote takeover flaws force risky patch windows and outages. |
Consumer breach exposure feeding enterprise credential abuse | 68% | 🔺 Rising | Fresh PII increases phishing realism and spray success. |
Public exploit releases accelerating attacker adoption | 66% | ➡ Stable | Leaked PoCs rapidly become scanner fuel and opportunistic compromise. |
Adobe Reader zero-day exploited in the wild (CVE-2026-34621) — If users can open PDFs from email, chat, or the web, this becomes a high-probability entry path; prioritize emergency patching and treat suspicious PDFs as zero-day delivery until fleet compliance is confirmed.
Marimo pre-auth RCE weaponized within hours (CVE-2026-39987) — Attackers moved fast after disclosure, which is exactly why “internal notebook platforms” need the same governance as internet-facing apps; assume exposed instances are already being scanned for Marimo-RCE.
Juniper Junos OS device-takeover class vulnerabilities — Critical network OS issues shift risk from “outage if we patch” to “takeover if we don’t,” especially when management planes are reachable; treat Junos-takeover as an exposure triage event, not routine maintenance.
Windows “BlueHammer” zero-day PoC leak accelerates abuse — When exploit code goes public, your patch/mitigation window shrinks dramatically because it becomes scanner bait; treat BlueHammer as a signal to tighten endpoint privilege boundaries and monitor for post-exploit behavior.
Dutch gym chain breach exposes customer data across EU countries — Fresh consumer exposure increases phishing precision and credential stuffing success (especially for employees using the same email/password habits everywhere); treat Basic-Fit fallout as a near-term identity defense driver.
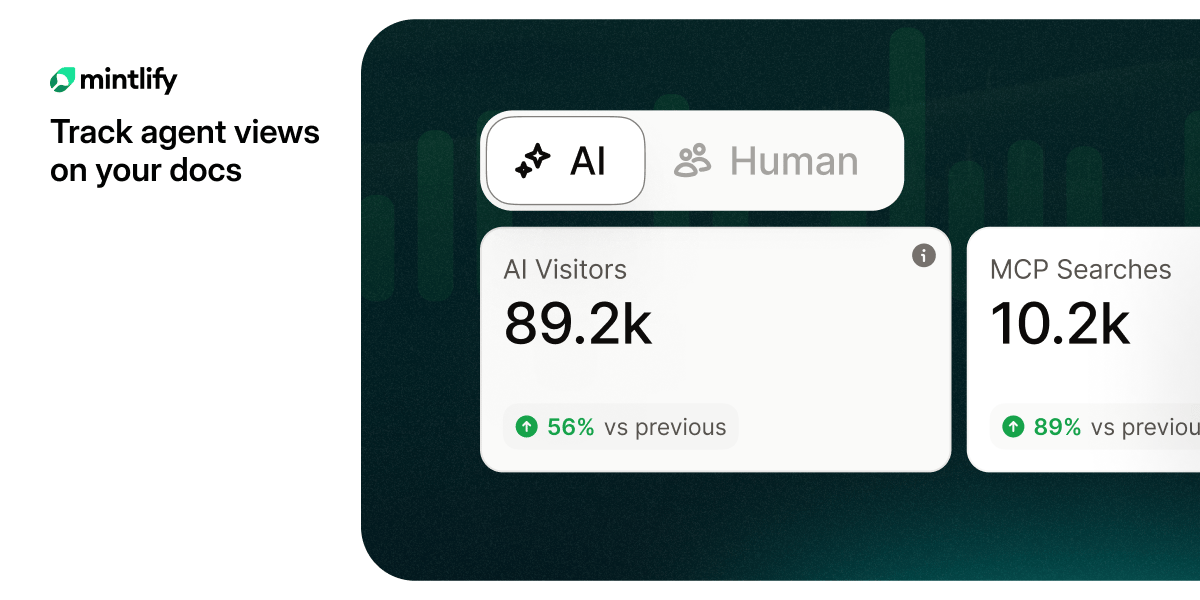
Are you tracking agent views on your docs?
AI agents already outnumber human visitors to your docs — now you can track them.
Endpoint exploitation is “low friction” again: attackers love file-format chains because they bypass perimeter assumptions.
Dev/data platforms are now frontline infrastructure: notebook tools are being treated like apps—because attackers can run code where your data already lives.
Network OS vulnerabilities amplify blast radius: a single compromised device can change routing, visibility, and trust paths.
Public PoCs turn targeted risk into commodity risk: you don’t need to be special—just exposed.
Consumer breaches become enterprise identity problems: phishing and credential abuse improve as soon as new datasets circulate.
Adobe/PDF containment: enforce rapid Reader updates, isolate attachment detonation workflows, and hunt for suspicious Reader child processes and post-open outbound connections.
Notebook platform governance: inventory Marimo (and similar) deployments, restrict exposure, patch immediately, and monitor for unexpected process execution and new admin/session artifacts.
Junos exposure triage: identify reachable management planes, prioritize patches for internet-adjacent devices, and enable configuration-change alerting (admin users, ACLs, routing changes).
PoC-driven defense posture: increase monitoring for privilege escalation behavior, suspicious local admin creation, and unexpected scheduled task/service creation following exploit attempts.
Credential abuse readiness: tune detection for spray/ATO patterns, enforce MFA, and prioritize awareness messaging where the new breach dataset is regionally relevant.
This week is about patch speed and patch proof.
“We applied the update” is not a control… verified compliance is.
Attackers aren’t outpacing you with genius; they’re outpacing you with time.
Shrink your window: patch fast, reduce exposure, and validate the outcome.
(Forward this to the SOC, endpoint owners, network engineering, and identity leadership to align emergency patching, exposure triage, and credential-abuse readiness.)
88% resolved. 22% loyal. Your stack has a problem.
Those numbers aren't a CX issue — they're a design issue. Gladly's 2026 Customer Expectations Report breaks down exactly where AI-powered service loses customers, and what the architecture of loyalty-driven CX actually looks like.