- Mycomputerspot Security Newsletter
- Posts
- Market & Momentum - 04/06/2026
Market & Momentum - 04/06/2026
This week opens with sharpened enterprise risk around automated web-app exploitation, exploited endpoint-management infrastructure, and supply-chain poisoning in developer ecosystems—showing how attackers are scaling access while defenders are still arguing about patch windows.
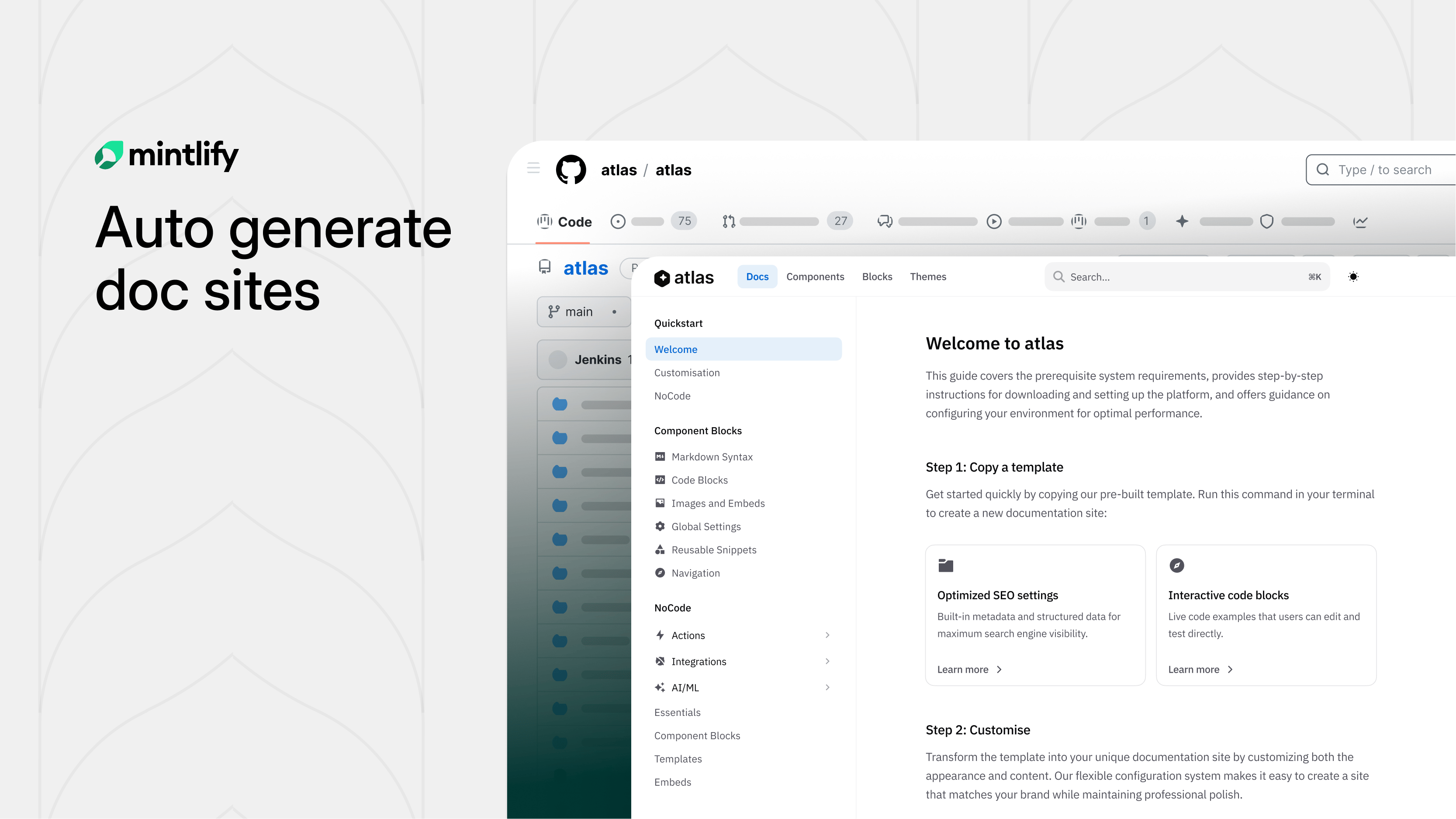
Your Docs Deserve Better Than You
Hate writing docs? Same.
Mintlify built something clever: swap "github.com" with "mintlify.com" in any public repo URL and get a fully structured, branded documentation site.
Under the hood, AI agents study your codebase before writing a single word. They scrape your README, pull brand colors, analyze your API surface, and build a structural plan first. The result? Docs that actually make sense, not the rambling, contradictory mess most AI generators spit out.
Parallel subagents then write each section simultaneously, slashing generation time nearly in half. A final validation sweep catches broken links and loose ends before you ever see it.
What used to take weeks of painful blank-page staring is now a few minutes of editing something that already exists.
Try it on any open-source project you love. You might be surprised how close to ready it already is.
Over the weekend, threat signals converged on five patterns: automated exploitation of popular web stacks for credential theft, active exploitation against enterprise management servers, registry/package poisoning targeting developers, high-confidence state-linked social engineering against high-value financial systems, and trusted-update-chain abuse in on-prem collaboration tooling. Operationally: your highest risk is coming from internet-facing apps, “management plane” systems, and developer supply chains…
The exact places where compromise turns into a broad, fast blast radius.

Trend (Macro) | Likelihood | Direction | Signal for the Week |
|---|---|---|---|
Automated exploitation of web apps for credential harvesting | 83% | 🔺 Rising | Scanning + exploitation is driving mass credential theft and follow-on access sales. |
Exploitation of enterprise management servers (EDR/EMS/admin tooling) | 78% | 🔺 Rising | Hotfix cycles + exposed instances = repeatable attacker wins. |
Developer supply-chain poisoning via package registries | 74% | 🔺 Rising | “Looks like a plugin” still beats human review at scale. |
State-linked social engineering targeting financial/crypto operations | 70% | 🔺 Rising | Pre-positioning + key compromise enables instant, massive theft. |
Trusted update-chain abuse in self-hosted platforms | 66% | ➡ Stable | If attackers can poison updates, endpoint compromise becomes a single push. |
Automated credential theft via Next.js “React2Shell” exploitation (CVE-2025-55182) — Large-scale campaigns are exploiting exposed apps to harvest credentials and map org infrastructure, making React2Shell a “patch-now + hunt-now” priority for any internet-facing Next.js footprint.
Fortinet FortiClient EMS flaw actively exploited (CVE-2026-35616) — EMS is a management plane, so compromise is leverage; the presence of exposed instances and active exploitation makes FortiClient-EMS a top-tier risk for enterprises running centralized endpoint management.
Malicious npm packages disguised as Strapi plugins — Researchers found dozens of fake plugins with postinstall payloads that target data stores and drop implants, turning dev dependencies into intrusion delivery via Strapi-plugins (the “one dev install = many downstream victims” math).
DPRK-linked social engineering behind $285M Drift heist — This is the modern playbook: long-prep targeting + key compromise + instant drain, and the speed of execution makes admin-key protection and privileged workflow monitoring a board-level control, not a niche crypto problem.
TrueConf update mechanism abused to distribute malware (CVE-2026-3502) — Attackers turned the trusted update flow into a distribution channel across connected environments, which is why update-trust failures are uniquely dangerous in self-hosted platforms.
CISA adds TrueConf Client flaw to KEV after active exploitation — When a vulnerability lands in KEV, it’s not theoretical; treat KEV as your “this is being used right now” patch justification for leadership.
Your AI is resolving tickets. Is it keeping customers?
Resolution rates look great. But Gladly's 2026 Customer Expectations Report reveals the metric most CIOs are missing — and what the data says about where AI investments actually translate into retention, not just throughput.
Web-app exploitation is being industrialized. Attackers aren’t “picking targets,” they’re harvesting whoever is exposed and selling or using access.
Management planes are the new crown jewels. EMS/endpoint tooling compromise collapses containment timelines and multiplies impact.
Supply chain is still the cheapest scaling strategy. Package registries remain a high-trust input with low review friction.
State actors keep winning with human targeting, not 0-days. Social engineering plus key compromise outperforms fancy malware when the goal is fast, high-value control.
Trusted updates are a single point of mass compromise. If attackers can poison distribution, endpoint takeover becomes a feature, not a bug.
React2Shell exposure sweep: identify all internet-facing Next.js services, confirm patch/mitigation status, and hunt for suspicious POST payload patterns, webshell-like artifacts, and abnormal auth/credential usage downstream.
FortiClient EMS hardening: patch/hotfix immediately, restrict EMS exposure, validate admin auth controls, and review audit logs for new accounts, token creation, and privileged action bursts.
Dependency governance: enforce allowlists for npm, block unknown “plugin” lookalikes, monitor CI/CD for new dependency introductions, and alert on postinstall script behavior.
Privileged key protection: tighten key custody workflows, require step-up auth for admin/key actions, monitor for anomalous nonce/transaction sequences (or equivalent high-velocity control actions in your environment).
Update-chain integrity checks: confirm update signature verification where supported, segment update servers, and monitor for tampered binaries and unexpected update pushes.
You don’t win weeks like this with “more alerts.”
You win with less exposure: fewer public apps, fewer reachable management planes, fewer ungoverned dependencies.
This week’s theme: scale beats brilliance. Attackers are scaling web exploitation, scaling supply-chain poisoning, and scaling trust abuse. Your counter is scalable governance: inventory, hardening, and verification that’s fast enough to matter.
J.W.
(P.S. Forward this to the SOC, app owners, endpoint management owners, and engineering leadership to align patch urgency, management-plane controls, and dependency governance.)
Are you tracking agent views on your docs?
AI agents already outnumber human visitors to your docs — now you can track them.