Can this idea actually make money?
The fastest way to find out is simple — launch a newsletter and website in minutes, then turn what you know into something people can buy.
With beehiiv’s Digital Product Suite, your expertise becomes real products: a short guide, a playbook, a set of templates, or limited access to your time. No friction, and no code required. Just create, price it, and share it with your audience.
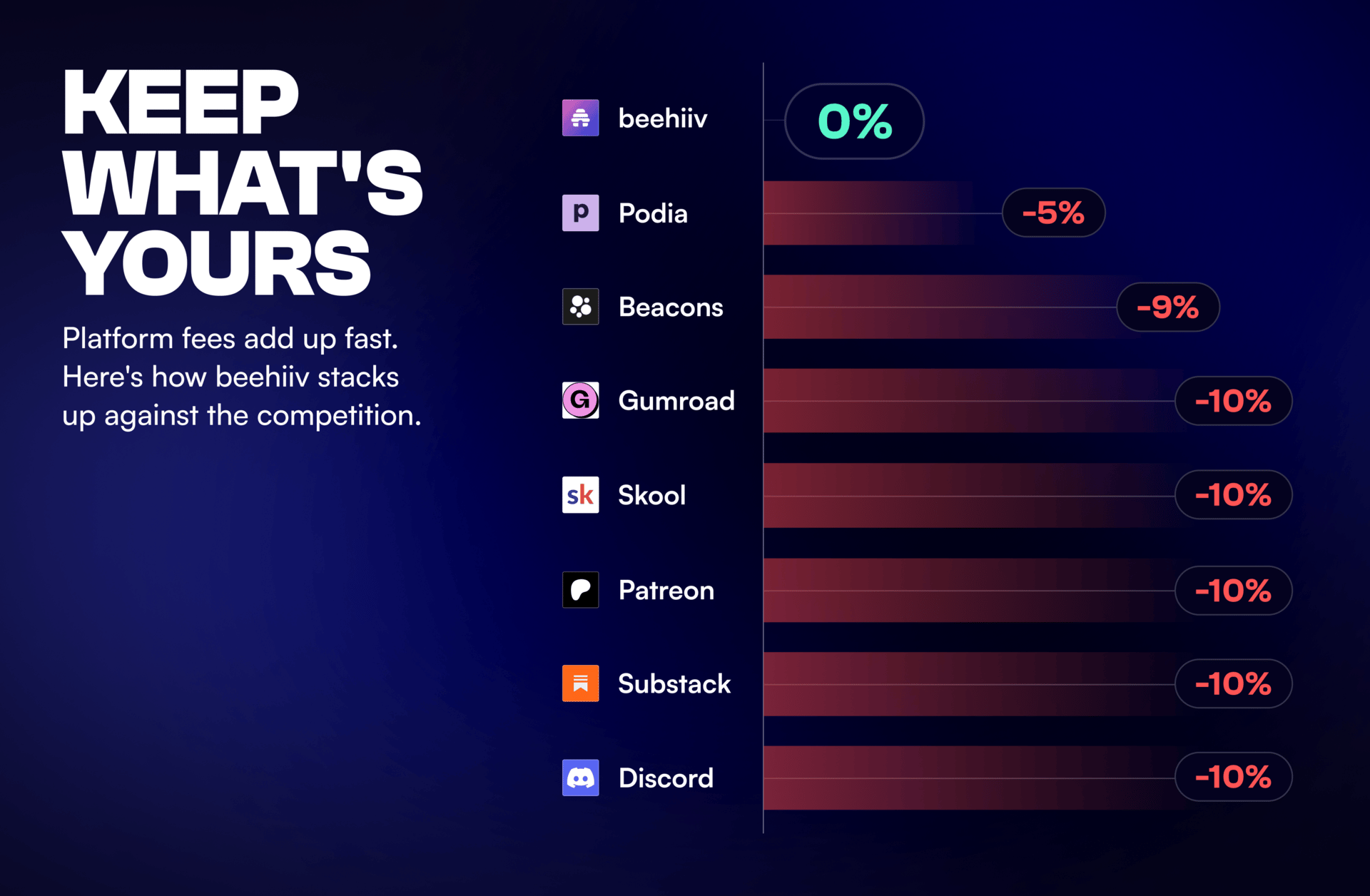
And unlike other platforms that quietly take 5–10% of every sale, beehiiv takes 0%. What you earn is yours to keep.
For a limited time, get 30% off your first 3 months on beehiiv with code PRODUCT30.
Over the last ~72 hours, threat signals converged on five patterns: ClickFix-style social engineering evolving into reliable malware staging, browser extension takeovers turning “productivity” into persistence, edge firewall vulnerability volume driving patch compression, web server exploitation chained with credential theft tooling, and mobile exploit-chain pressure via KEV expansion. The operational takeaway: defenders need to treat user execution paths and edge exposure as the same problem—because attackers already do.

Trend (Macro) | Likelihood | Direction | Signal for the Week |
|---|---|---|---|
User-assisted execution (ClickFix delivery chains) | 81% | 🔺 Rising | “You run it for them” keeps bypassing controls and spreading stealer/RAT payloads. |
Browser trust abuse (extension ownership takeovers) | 75% | 🔺 Rising | Legit extensions flipping malicious creates silent credential theft at scale. |
Firewall/edge patch compression (high vuln volume) | 73% | 🔺 Rising | Vendor patch bundles raise operational risk and downtime decisions. |
Web server exploitation + credential theft tooling | 70% | 🔺 Rising | Webshell-to-credential-theft patterns point to longer-dwell intrusions. |
Mobile exploit chains (KEV pressure on iOS flaws) | 62% | ➡ Stable | High-end targeting persists; exec/VIP risk remains elevated. |
Microsoft details ClickFix using Windows Terminal to drop Lumma Stealer — This is social engineering with a tuxedo on: users are guided into “legit-looking” command execution that deploys credential theft, making WindowsTerminal a high-signal hunt pivot for suspicious copy/paste command patterns.
Ransomware breaches tied to ClickFix + CastleRAT delivery — This shows the direct line from user-assisted execution to enterprise impact; treat Termite as confirmation that these lures are no longer “just stealer noise.”
Chrome extensions turning malicious after ownership transfer — The quiet part out loud: extensions can flip post-install without triggering the same controls as “new software,” making ownership-transfer a governance problem, not just a SOC problem.
Cisco discloses 48 firewall ecosystem vulnerabilities (including critical) — High-volume firewall advisories force ugly tradeoffs (patch windows vs. exposure), and attackers love when you postpone; prioritize Cisco-firewalls based on internet reachability and management-plane exposure.
New espionage cluster chaining web server exploits + Mimikatz — Webshell footholds plus credential dumping is the classic “set up camp” pattern; if you own IIS/inetpub environments, Mimikatz is your cue to hunt for webshell artifacts, odd worker process behavior, and suspicious LSASS access.
CISA expands KEV with iOS flaws linked to a nation-state exploit kit — Mobile targeting remains an executive risk multiplier; if you protect leadership devices, treat iOS-KEV as justification to tighten update enforcement and mobile telemetry review.
Attio is the AI CRM for modern teams.
Connect your email and calendar and Attio instantly builds your CRM. Every contact, every company, every conversation — organized in one place. Then ask it anything. No more digging, no more data entry. Just answers.
ClickFix is maturing into a dependable enterprise access path—it scales because it turns the user into the execution mechanism.
Browser trust is the new perimeter—extension ecosystems are being abused like software supply chain, but faster and quieter.
Firewall patching is becoming an availability-versus-exposure decision weekly—and attackers plan around your maintenance calendar.
Web server exploitation remains the “quiet front door” for espionage and long-dwell intrusion because it blends into normal admin reality.
Mobile exploit chains stay strategically valuable—especially for VIP targeting, surveillance, and identity takeover.
ClickFix containment: alert on unusual Windows Terminal usage, suspicious clipboard-driven command execution, child-process anomalies, and outbound traffic spikes immediately after terminal sessions.
Extension governance: move to an allowlist model where possible; monitor for extension updates that introduce new permissions or remote control behavior; audit “recently updated” extensions org-wide.
Firewall exposure triage: inventory which devices are externally reachable (including management planes), patch the most exposed first, and add config-change monitoring for admin accounts and remote management toggles.
Web server hardening + hunts: look for unexpected file writes in web roots, new/modified ASPX artifacts, unusual w3wp behavior, and credential dumping indicators (LSASS access, suspicious toolmarks).
Mobile exec posture: enforce minimum patch levels, restrict sideloading, and tighten conditional access for high-risk users; treat mobile telemetry as first-class IR input.
If your users can be tricked into running the payload, and your browser can be tricked into becoming the implant, then the only winning move is governance that’s fast enough to matter.
This week’s reality: attackers are abusing trust surfaces (users, browsers, firewalls) more than they’re exploiting “mystery malware.” Reduce trust, increase verification, and the week gets a lot quieter.
J.W.
(P.S. Forward this to the SOC, endpoint owners, and infrastructure leadership to align user-execution controls, browser governance, and edge patch urgency.)
You think 4x faster than you type. Why slow down?
Wispr Flow turns your voice into ready-to-send text inside any app. Speak naturally and Flow handles the cleanup -- stripping filler words, fixing grammar, formatting everything properly.
For developers, this means:
Dictate into Cursor, VS Code, or any IDE with full syntax accuracy
Give coding agents 10x more context by talking instead of typing
Write PRs, docs, and Linear tickets without switching to a text editor
Respond to Slack and email without breaking your flow state
Used by teams at OpenAI, Vercel, and Clay. 89% of messages sent with zero edits. Millions of users worldwide.
Available on Mac, Windows, iPhone, and now Android - free and unlimited on Android during launch.