Voice dictation that doesn't mangle your syntax.
Most dictation tools choke on technical language. Wispr Flow doesn't. It understands code syntax, framework names, and developer jargon - so you can dictate directly into your IDE and send without fixing.
Use it everywhere: Cursor, VS Code, Slack, Linear, Notion, your browser. Flow sits at the system level, so there's nothing to install per-app. Tap and talk.
Developers use Flow to write documentation 4x faster, give coding agents richer context, and respond to Slack without breaking focus. 89% of messages go out with zero edits.
Millions of users worldwide. Now on Mac, Windows, iPhone, and Android (free and unlimited on Android during launch).
Over the last ~72 hours, the threat signal is clustering around five patterns: state-linked exploitation of Windows components, browser-native AI feature abuse, local AI agent hijacking from a web page, cloud API key overreach driving cost + data exposure, and large breach datasets re-entering the market.
Translation: your perimeter isn’t the only problem…
Your endpoints, browsers, and “helpful” automation layers are now prime real estate.

Trend (Macro) | Likelihood | Direction | Signal for the Week |
|---|---|---|---|
Windows client-side exploitation via phishing delivery chains | 80% | 🔺 Rising | Shortcut/HTML delivery keeps bypassing “we have EDR” confidence. |
AI feature abuse inside browsers (privileged assistant surfaces) | 72% | 🔺 Rising | Extensions + AI panels create new data access paths. |
Local AI agent hijack / localhost abuse | 70% | 🔺 Rising | Web pages shouldn’t be able to “talk” to your local tools… yet here we are. |
Cloud API key abuse (quota theft + data access) | 68% | 🔺 Rising | “It’s just an API key” is still the most expensive sentence in cloud. |
Breach dataset recycling fueling credential abuse | 65% | ➡ Stable | Old breach, new phishing, same Monday morning cleanup. |
APT28 linked to MSHTML security feature bypass (CVE-2026-21513) — Akamai findings suggest Russia-linked activity tied to pre-patch exploitation paths, meaning Windows fleets should treat this as a MSHTML-zero-day risk until patch coverage is verified end-to-end.
Chrome AI assistant feature could be hijacked by malicious extensions — A flaw impacting Chrome’s Gemini Live assistant highlights how “helpful” browser features can become privileged access for data theft, turning extensions into a stealth Gemini-hijack path.
OpenClaw ‘ClawJacked’ lets a malicious website take over local AI agents — If developers or power users run OpenClaw locally, a drive-by site visit could brute-force and seize the agent, making ClawJacked the kind of “one tab, one takeover” problem you don’t see coming in traditional threat models.
Thousands of public Google Cloud API keys gained Gemini access after API enablement — Research found exposed keys could authenticate to Gemini endpoints and rack up usage or access sensitive data, meaning your “public” billing tokens may now be Gemini-credentials without anyone explicitly approving that blast radius.
Canadian Tire breach dataset resurfaces at massive scale (38M+ accounts) — Even when a breach is “old news,” its downstream impact is current: fresh data dumps raise phishing realism and credential stuffing success, making CanadianTire-data relevant for any org with Canadian customers, employees, or partners.
Madison Square Garden confirms breach tied to Oracle EBS campaign — Confirmation months later reinforces a hard truth: third-party enterprise platforms can become the shared weakness for dozens of orgs, and the long tail of disclosures keeps Oracle-fallout alive well after the initial intrusion window.
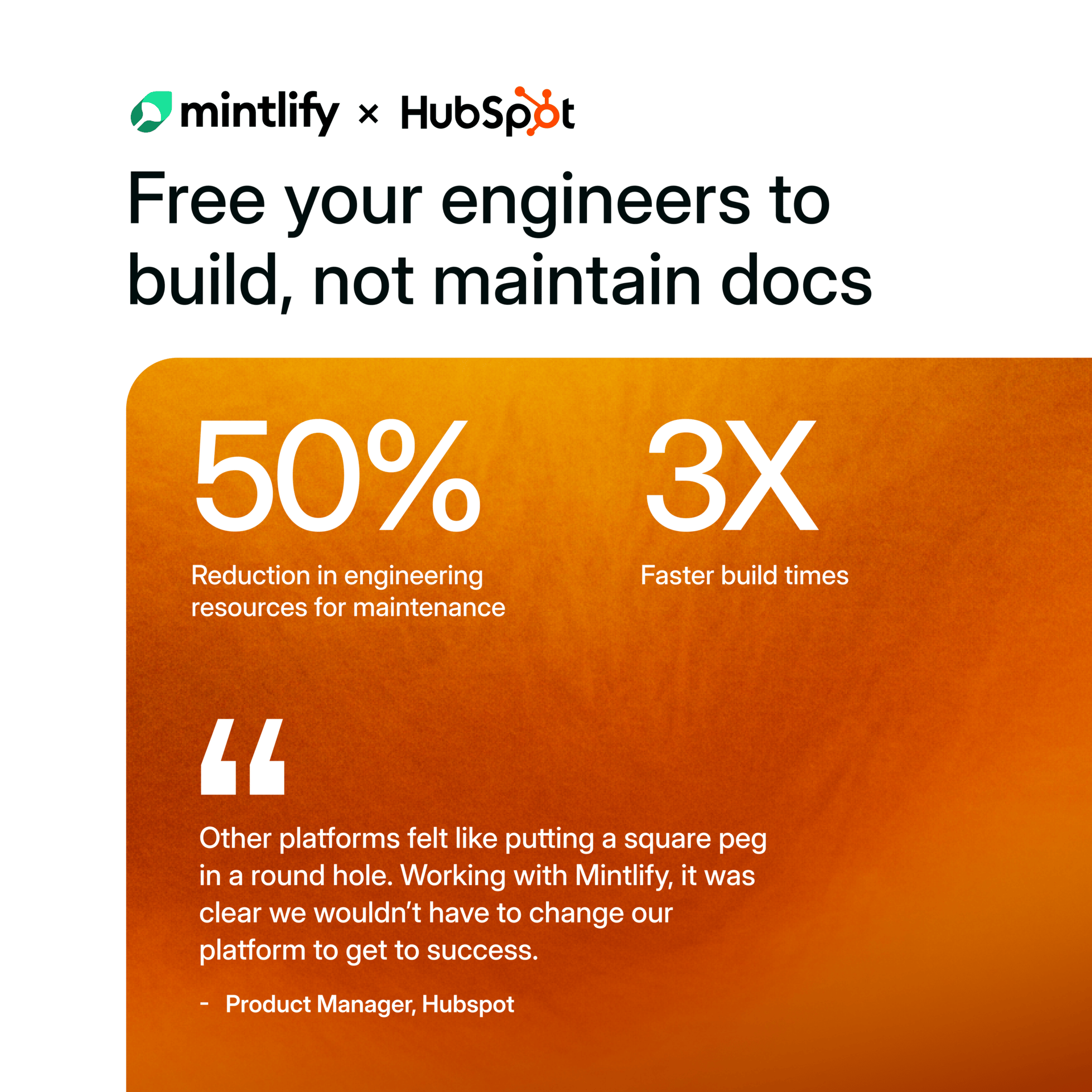
See Why HubSpot Chose Mintlify for Docs
HubSpot switched to Mintlify and saw 3x faster builds with 50% fewer eng resources. Beautiful, AI-native documentation that scales with your product — no custom infrastructure required.
Windows delivery chains are still printing money for nation-state operators: the “convince the user to click” model remains brutally effective.
Browser + AI convergence is expanding privilege in places defenders don’t traditionally monitor (assistant panels, extension permission sets, local file access).
Localhost is becoming a new battleground: if a web page can talk to local services, attackers will treat it like a remote interface.
Cloud risk is dynamic, not static: turning on one service can silently raise the privilege of old keys and old deployments.
Breach data is a force multiplier: it doesn’t need to be “fresh” to be operationally useful for phishing and account takeover.
Patch proof, not patch hope: confirm Windows update coverage for February fixes tied to CVE-2026-21513; validate via telemetry (not spreadsheets).
Browser governance: enforce managed Chrome updates, restrict extension installs, and aggressively review extensions requesting broad permissions—especially those interacting with AI side panels.
Local AI tooling guardrails: block/limit local agent gateways where possible, require strong secrets, enable rate limiting on localhost, and monitor for unexpected WebSocket activity.
API key containment: inventory Google API keys exposed in client-side code and public repos; rotate oldest first; lock keys to specific APIs, IPs, and referrers.
Credential abuse readiness: increase monitoring for spray patterns and anomalous logins; refresh high-risk user phishing guidance (execs, finance, IT, devs).
Third-party blast-radius review: if you run Oracle EBS or similar enterprise platforms, demand vendor patch attestations and validate what data is reachable from those systems.
You don’t need a bigger SOC.
You need fewer “unknowns”: unknown patches, unknown extensions, unknown API keys, unknown local services.
Attackers live in the gaps you don’t inventory.
If your browser can reach your files, and your web page can reach your local tools, then “endpoint security” just became “everything security.”
J.W.
(P.S. Forward this to the SOC, endpoint owners, cloud leadership, and the CISO council to align patch urgency, browser governance, and API key controls.)
World’s First Safe AI-Native Browser
AI should work for you, not the other way around. Norton Neo is the world's first safe AI-native browser with context-aware AI, built-in privacy, and configurable memory. Zero-prompt productivity that actually works.