In the last ~48 hours, key cybersecurity developments require executive attention: Cisco SD-WAN controller exploitation enabling admin-level access, a Microsoft Exchange zero-day actively exploited in the wild, fallout from the TanStack software supply-chain compromise impacting developer environments, and a Foxconn ransomware incident disrupting North American manufacturing operations.
These developments reinforce priority themes for the weekend: trusted infrastructure is becoming attacker infrastructure, developer ecosystems remain a high-value credential target, and operational disruption is increasingly the end goal—not just data theft.
Escape Wall Street's Control Over Your Crypto
Wall Street hijacked the stock market 200 years ago.
Now in 2026, they're coming for YOUR digital assets.
Bitcoin was supposed to be peer-to-peer. No banks. No middlemen.
Not anymore.
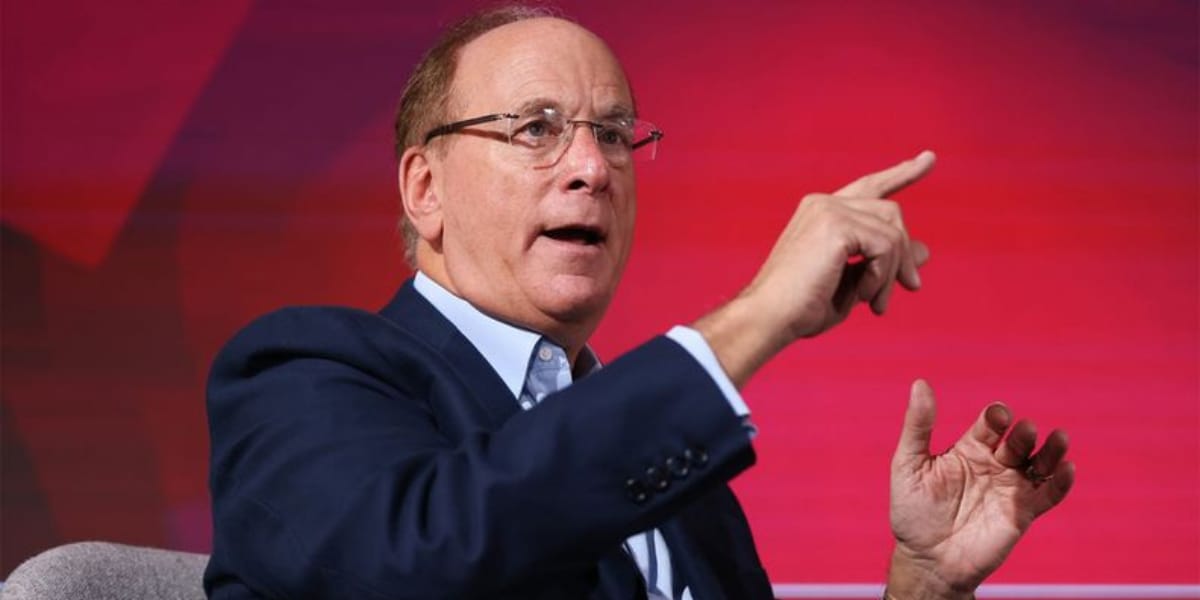
BlackRock owns more Bitcoin than most countries.
Fidelity's ETF hit $10 billion.
JPMorgan called Bitcoin a "fraud" — now they run billions in tokenized assets.
They ARE crypto now.
Every time you hit "Buy" on Coinbase, you're trading at their prices that they've already positioned themselves for the biggest returns. You're fighting over scraps.
It's the 2008 playbook.
Wall Street sold mortgage-backed securities to retail, then shorted them and made billions while people lost their homes.
But there's a way to operate outside their system.
Tan Gera, ex-Wall Street banker and CFA Charterholder, walked away after discovering their two-tier system.
Now, his 35-person research team helps 3,000+ investors access opportunities before Wall Street marks them up 100x.
For educational purposes only. Results will vary. DM Intelligence LLC is not liable for losses.

Top-level takeaways this week:
Edge / SD-WAN Infrastructure ↑ — SD-WAN control-plane compromise risk continues escalating.
Email & Identity Infrastructure ↑ — Exchange remains one of the most valuable enterprise footholds.
Developer Supply Chain ↑ — Dependency poisoning and package compromise continue targeting CI/CD trust paths.
Manufacturing & Operational Continuity ↑ — Foxconn incident reinforces supply-chain disruption risk.
1) Cisco SD-WAN controller auth bypass exploited – High
What changed: Cisco patched an exploited Catalyst SD-WAN Controller vulnerability allowing attackers to gain administrative access to controller infrastructure.
Why this matters: SD-WAN is a control plane. If attackers compromise it, they can manipulate routing, network segmentation, and visibility while defenders argue whether it’s “just a network issue.”
2) Microsoft warns of Exchange Server zero-day – High
What changed: Microsoft issued guidance for an exploited Exchange Server zero-day while organizations await a permanent fix.
Why this matters: Exchange combines identity, communications, and internal trust. Compromise here becomes organizational compromise extremely fast.
3) OpenAI / TanStack supply-chain attack – Medium-High
What changed: OpenAI disclosed impact tied to the TanStack software supply-chain compromise after malicious package artifacts exposed credential material from development workflows.
Why this matters: Developer ecosystems now function as operational attack surfaces. Poison the dependency chain and developers will deploy the compromise for you.
4) Foxconn confirms ransomware attack – Medium-High
What changed: Electronics manufacturer Foxconn confirmed a ransomware attack on North American factories after attackers claimed theft of roughly 8 TB of data.
Why this matters: Manufacturing attacks create operational disruption, supplier instability, delivery delays, and direct revenue pressure. This is a business continuity risk at enterprise scale.
Stage | Vector | What We’re Seeing |
|---|---|---|
Initial Access | Edge infrastructure exploitation | SD-WAN controller auth bypass enabling administrative access |
Persistence / Identity | Exchange infrastructure compromise | Email and identity-layer footholds remain high-value targets |
Supply Chain | Dependency/package compromise | Malicious package artifacts exposing developer credentials and CI/CD access |
Impact | Manufacturing disruption | Ransomware operations targeting operational continuity and supplier ecosystems |
Stop re-prompting. Say it right the first time.
Voice-first prompts preserve the nuance you cut when typing. Speak once, paste into any AI tool, get results that don't need a follow-up. 89% of messages sent with zero edits.
🔄 Patch & Hardening
Patch Cisco SD-WAN controllers immediately and restrict management-plane access.
Apply Microsoft Exchange mitigations and validate exposed systems.
Freeze high-risk dependency updates tied to TanStack-related packages until validated.
Validate immutable backups and operational recovery readiness for manufacturing and supplier-facing systems.
🧑💻 People & Monitoring
Monitor SD-WAN admin activity, config changes, and rare-source logins.
Hunt Exchange logs for abnormal mailbox access and suspicious web requests.
Monitor developer environments for package drift, CI token usage, and unusual outbound traffic.
Watch manufacturing and supplier portals for anomalous access and large transfers.
📋 Process
Enforce change freeze on SD-WAN, Exchange, and CI/CD infrastructure unless CISO-approved.
Conduct 30-minute tabletop: “Supply-chain compromise → credential theft → Exchange foothold → SD-WAN access → operational disruption.”
🤝 Partners
Require MSP attestation for SD-WAN and Exchange remediation status.
Require platform teams to confirm package integrity and credential rotation.
Validate supplier exposure and continuity dependencies tied to manufacturing operations.
SD-WAN configuration changes outside maintenance windows
Exchange mailbox access anomalies and suspicious web requests
Dependency lockfile drift, package hash changes, and unusual CI/CD token usage
Large outbound transfers from supplier and manufacturing environments
Overall: High
This weekend’s highest-risk pattern is trusted-system compromise:
SD-WAN controllers
Exchange infrastructure
Developer ecosystems
Manufacturing operations
Attackers increasingly target the systems organizations assume are inherently trustworthy.
SD-WAN infrastructure should be treated like Tier-0 identity systems
Exchange compromise remains one of the fastest routes to organizational impact
Developer ecosystems are now credential pipelines and operational attack surfaces
Manufacturing attacks create business continuity risk far beyond the affected company
🔄 Verify: SD-WAN and Exchange remediation status
📊 Validate: Monitoring coverage across edge, Exchange, CI/CD, and supplier systems
💼 Confirm: Credential rotations and dependency integrity reviews are complete
🔹 Rehearse: “Trusted-platform compromise → operational disruption” response scenarios
Final Insight: Attackers are no longer trying to break through your defenses.
They’re targeting the systems your defenses already trust.
Copy BlackRock's $10 Trillion Playbook
BlackRock manages $10 trillion using a playbook hidden from retail investors - until now.
The ABN Framework reverse-engineers their three-phase system: protect your base, collect fees like a bank, and get into markets before major listings.
4,000+ investors are already using it but the window is closing.
For educational purposes only. Results will vary. DM Intelligence LLC is not liable for losses.